RESOURCE CENTER
From analyst reports to eBooks and videos to webinars, we have all the data protection content you need.
From analyst reports to eBooks and videos to webinars, we have all the data protection content you need.
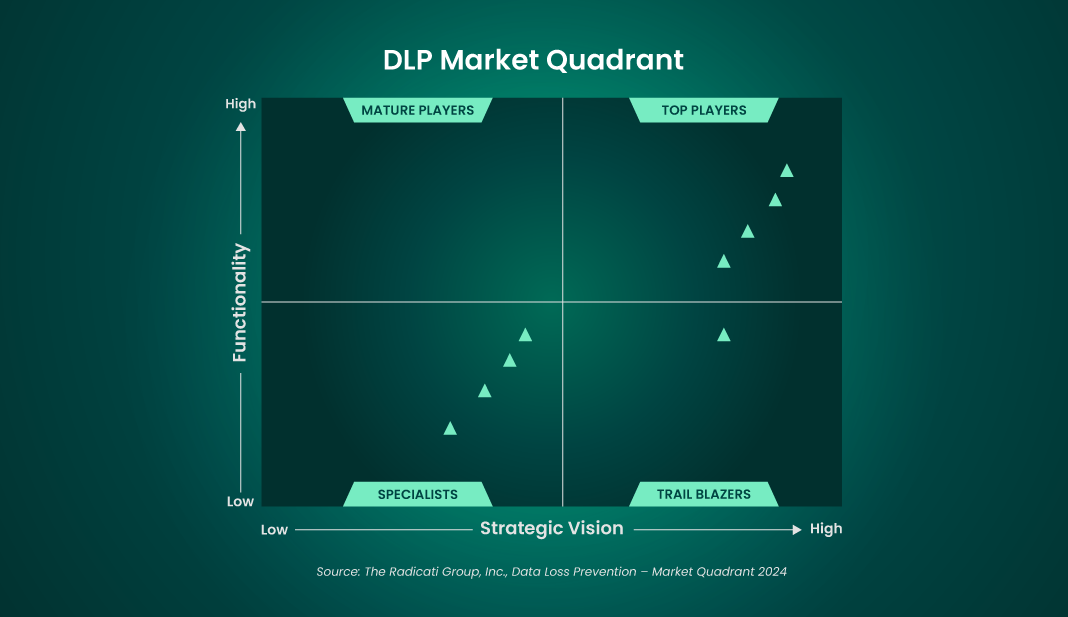
The 2024 Data Loss Prevention Market Quadrant
GigaOm Radar for DLP

SC Media Labs 2020 DLP Group Test & DG Product Review