Court Sides with Insurer: Credit Card Data isn’t Lost Property
A court in Alabama threw out a suit brought by a breached grocery store chain, saying that stolen credit card data doesn’t count as “damaged property.”
Cyber Needs More Perp Walks
The arrest of a 29-year-old man in Prague for suspected involvement in the 2012 hack of LinkedIn is a big victory for law enforcement. Even more important: viral video of the arrest.
Sign Up with the Usual Suspects: Consumer Breach Response is Broken and How to Fix It
The scourge of data breaches and identity theft is more than a decade old. But our tools for dealing with these common incidents are outdated and ineffective. Why?
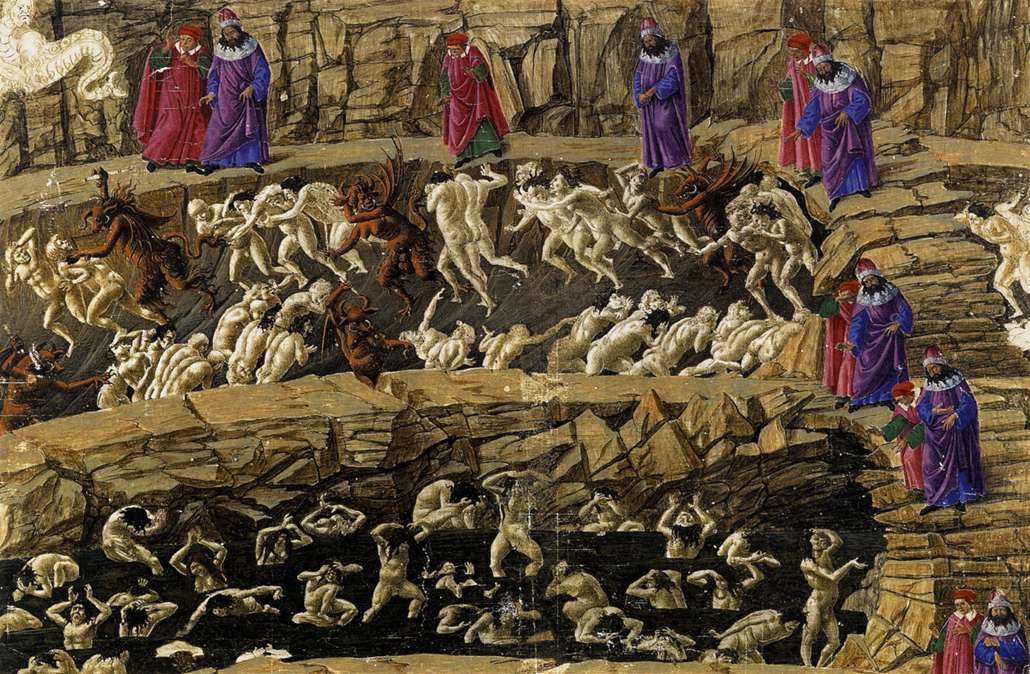
Circle in Hell Awaits Habitat for Humanity Hackers
The Colorado branch of Habitat for Humanity says a long-running and “malicious” data breach started with ransomware in June, and is making it hard to even conduct business.
Yahoo Breach: User Data Considered Toxic
Computer science and security rely on precision for the descriptions of their constructs and concepts. But there are some things that defy description in these realms, and the Yahoo data breach is one of them.
Rarely is the (Breach) Question asked: Is Our IT Pros Learning?
A new survey by The SANS Institute suggests that companies are worried about data breaches – but aren’t doing much to prevent them.
Once More Into the Breach Response
Reasonable people can, and often do, disagree about what constitutes a proper public response to a data breach. Some people want immediate and full disclosure of all of the details of the event, while others tend to favor a more measured approach, releasing some information at the beginning and more data as things shake out.
Down Under, Lawmakers Ponder Pain and Suffering from Breaches
Should businesses be liable for the pain and suffering experienced by customers as the result of a data breach? Lawmakers in Australia say “yes.”
Carded: Hack of Medical ID Card Provider Affects 3.3M
The hack of Newkirk Products, a little known provider of medical ID cards, underscores the dangers third parties pose to regulated health data.
Paid in Full: Why the MICROS Data Breach Could be More than Meets the Eye
Data breaches come in all shapes and sizes. Some, like the attacks on Target and Home Depot, are big, public, and expensive. Others can be small and quiet, but no less expensive in the long run.
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!