In 2016, it seemed like data breaches were making national headlines every other week, exposing the consumer data of anywhere from a few thousand people to hundreds of millions. It was certainly the most dramatic year yet from a cybersecurity perspective, surpassing 2014’s total number of records exposed (1 billion) in just its largest single breach. Interestingly, Forrester found that just three industries accounted for 95% of all breached customer records: technology (68%), government (16%), and retail (11%). It’s likely these industries will be the remain three major targets of cybercrime in 2017 due to the large caches of personally identifiable information (PII) they hold, but could there be even bigger unexpected targets? A closer inspection of the most notable events of 2016 just might provide some insight.

1. Yahoo!
Any conversation about major data breaches that occurred in 2016 must start with Yahoo!. With two major breaches revealed during the year, the company captured the record for the largest breach ever in September 2016 when 500 customer records were exposed and went on to break their own record by double that amount, announcing in December 2016 a previously undisclosed breach that affected one billion users of the site. The data exposed included dates of birth, email addresses, physical addresses, and security questions and answers. The most interesting reveal from these breaches was that the theft was not new; the crimes had taken place in 2014 and 2013, respectively, and were just discovered in 2016. Yahoo! has yet to disclose who committed the attacks, but hinted at a state-sponsored attacker in a statement on one of the incidents.
2. Democratic Party
The various hacks of the Democratic party in 2016, including the Democratic National Committee, Democratic Congressional Campaign Committee, and the chairman of the 2016 Hillary Clinton presidential campaign, John Podesta, rocked headlines and inspired serious debates about Russia’s involvement in the U.S. election. U.S. intelligence agencies have recently concluded that actors affiliated with the Russian government were in fact responsible for hacking the DNC and Podesta’s account, though there have been mixed messages from the President-elect on these findings.

Image via FX Tribune
3. FriendFinder Networks
The parent company of sites including Adult Friend Finder, Cams.com, and Penthouse.com, FriendFinder Networks was responsible for more than 412 million breached records in 2016. For perspective, that’s more than 10 times the amount of data exposed in the Ashley Madison breach of 2015. Sensitive data including usernames, emails addresses and passwords were accessed through a local file inclusion exploit, which gave the hackers to access all of the network’s sites.

4. Myspace
Millions of passwords for users of the once-popular social networking site Myspace were stolen by a hacker in May 2016. The attacker sold 427 million passwords for 360 million users on the dark web, endangering the many people who reuse their passwords across accounts. Like the Yahoo! breach, it seems that the intrusion took place in 2013, and as a result, likely affected many who may have thought their data was safe, given their lack of activity on the site in recent years.

5. LinkedIn
That same Myspace hacker has been connected to the person who breached 117 million records held by LinkedIn in May 2016. A Russian hacker who goes by the name “Peace” advertised the sale of email and password combinations for LinkedIn users on a dark web marketplace at a rate of five Bitcoins, or about $2,300. In addition to the Myspace and LinkedIn data breaches, Peace was responsible for various other cybercrimes revealed in 2016, including creating a backdoor in Linux Mint operating system that tricked users into downloading a malicious version of the program.
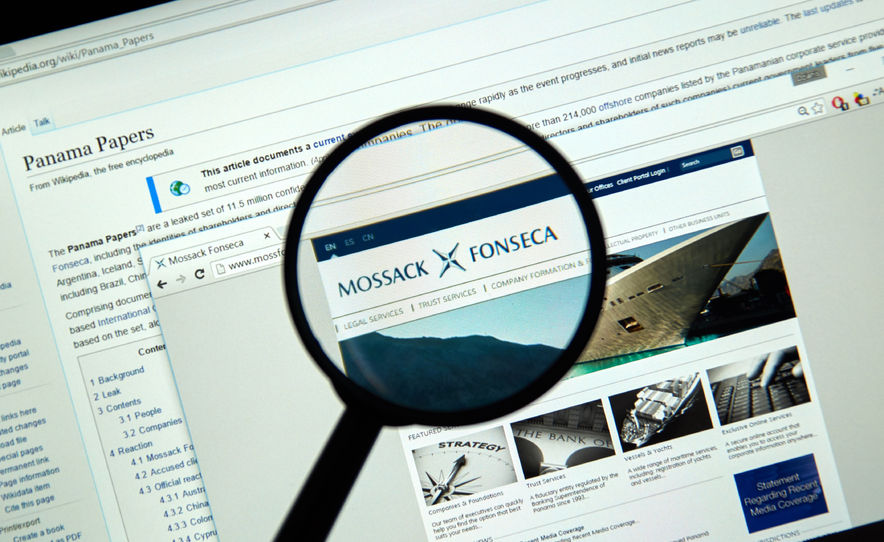
6. Mossack Fonseca/The Panama Papers
Panamanian law firm Mossack Fonseca suffered a data breach in April 2016 that exposed 2.6 terabytes of sensitive data totaling 11.5 million files. The leaked data included 4.8 million emails, 2.2 million PDF documents, 1.1 million image files, 3 million database records, and 320,000 other text files. Many of the details of the breach – including the attacker(s) behind it – remain unclear, but the leaked files exposed massive tax evasion operations involving wealthy individuals in over 200 countries and territories as well as several major security shortcomings at the firm, which had previously touted its strength in ensuring client privacy.

Image via Wikimedia Commons
7. National Security Agency (NSA)
The NSA had two major breaches during 2016, including the theft of 50 terabytes of data by a former staffer and the sale of NSA exploits and software by hacking group Shadow Brokers. In the case of the Shadow Brokers, the group stole a cache of advanced exploits used by the state-sponsored Equation Group, which they are now attempting to sell for bitcoin. These incidents put focused attention on the power that insider or outsider threats can hold if they gain access to troves of government data.

8. VK
Russian social media platform VK – often called “Russia’s Facebook” – was yet another company to fall victim to hacker Peace’s efforts in 2016. In June news broke that over 100 million user account credentials were being traded on the dark web. Peace shared 100,544,934 user records with Vice’s Motherboard publication to confirm the breach and listed the records for sale on The Real Deal dark web marketplace for one bitcoin. The breach also exposed poor security at VK, as the breached passwords were found to be stored in plain text.
