As it has been recently reported in numerous media sources, there is a new threat to Android phones called Stagefright. It takes advantage of a feature in text message apps that can allow for the automatic downloading of multimedia files in texts. This means that malicious code can be downloaded to an Android phone without any action being taken on the part of the phone owner other than opening a text message with an infected multimedia file.
Although a patch for this problem is not widely available from the major cell carriers there is a simple fix that will stop the “auto download” aspect of the Stagefright vulnerability. The fix will stop the auto-retrieval of media messages in your text message app.
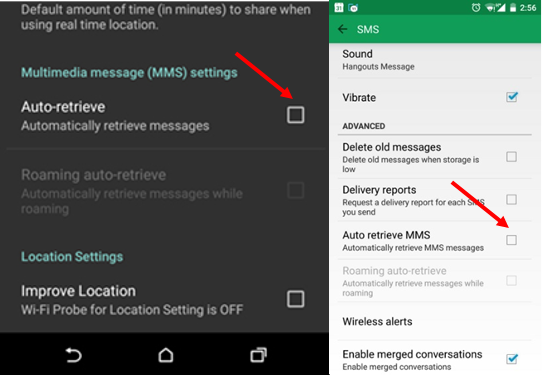
The particulars may vary from device to device but the general instructions for turning off auto-retrieval is as follows - please make this change ASAP to minimize the potential for infection:
- Go to Settings in your phone and from there the Application or Apps option.
- Find the Messages or Messaging and from there go to the Multimedia messages settings.
- Uncheck the Auto retrieve - automatically retrieve messages option.
Alternatively you can open your text app directly and navigate to the top level app Settings. Within Settings you should be able to access multimedia message settings.
Here are two examples of the setting that needs to be unchecked:
Images via CBS News and PC Magazine.
Even after applying this fix it is still necessary for all Android users to apply to text messages the same level of healthy skepticism that they should be using in relation to unsolicited emails. Whenever possible it is best to ignore or delete texts from those that you don’t know or are not expecting. Never download files or follow links in texts from those you don’t know.
