A Definition of HIPAA Compliance
The Health Insurance Portability and Accountability Act (HIPAA) sets the standard for sensitive patient data protection. Companies that deal with protected health information (PHI) must have physical, network, and process security measures in place and follow them to ensure HIPAA compliance. Covered entities (anyone providing treatment, payment, and operations in healthcare) and business associates (anyone who has access to patient information and provides support in treatment, payment, or operations) must meet HIPAA compliance. Other entities, such as subcontractors and any other related business associates, must also be in compliance.
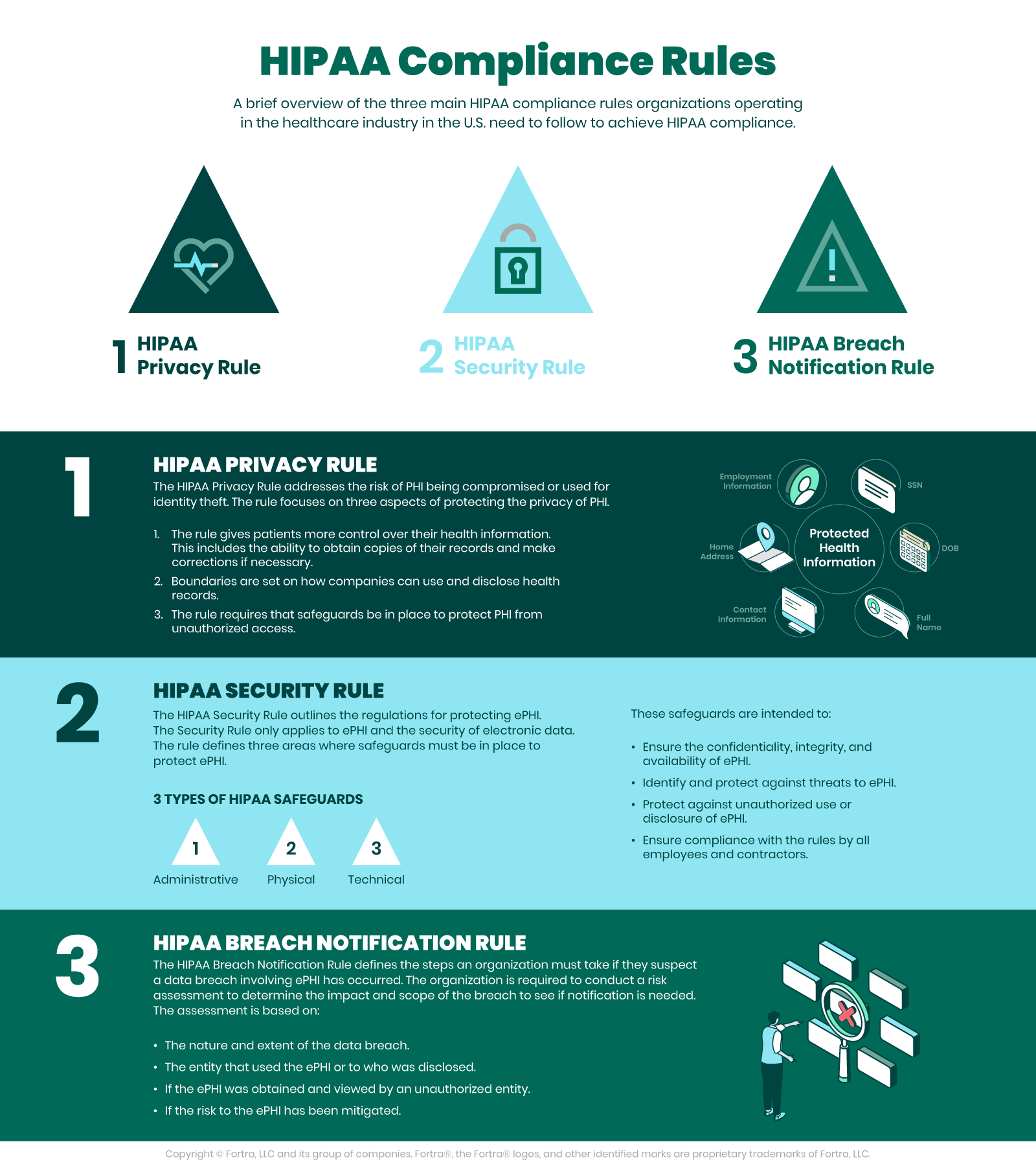
The HIPAA Privacy and HIPAA Security Rules
According to the U.S. Department of Health and Human Services (HHS), the HIPAA Privacy Rule, or Standards for Privacy of Individually Identifiable Health Information, establishes national standards for the protection of certain health information. Additionally, the Security Rule establishes a national set of security standards for protecting specific health information that is held or transferred in electronic form.
The Security Rule operationalizes the Privacy Rule’s protections by addressing the technical and nontechnical safeguards that covered entities must put in place to secure individuals’ electronic PHI (ePHI). Within HHS, the Office for Civil Rights (OCR) is responsible for enforcing the Privacy and Security Rules with voluntary compliance activities and civil money penalties.
The Need for HIPAA Compliance
HHS points out that as health care providers and other entities dealing with PHI move to computerized operations, including computerized physician order entry (CPOE) systems, electronic health records (EHR), and radiology, pharmacy, and laboratory systems, HIPAA compliance is more important than ever. Similarly, health plans provide access to claims as well as care management and self-service applications. While all of these electronic methods provide increased efficiency and mobility, they also drastically increase the security risks facing healthcare data.
The Security Rule is in place to protect the privacy of individuals’ health information, while at the same time allowing covered entities to adopt new technologies to improve the quality and efficiency of patient care. The Security Rule, by design, is flexible enough to allow a covered entity to implement policies, procedures, and technologies that are suited to the entity’s size, organizational structure, and risks to patients’ and consumers’ ePHI.
Physical and Technical Safeguards, Policies, and HIPAA Compliance
The HHS requires physical and technical safeguards for organizations hosting sensitive patient data. These physical safeguards include…
- Limited facility access and control with authorized access in place
- Policies about use and access to workstations and electronic media
- Restrictions for transferring, removing, disposing, and re-using electronic media and ePHI
Along the same lines, the technical safeguards of HIPAA require access control allowing only for authorized personnel to access ePHI. Access control includes…
- Using unique user IDS, emergency access procedures, automatic log off, and encryption and decryption
- Audit reports or tracking logs that record activity on hardware and software
Other technical policies for HIPAA compliance need to cover integrity controls, or measures put in place to confirm that ePHI is not altered or destroyed. IT disaster recovery and offsite backup are key components that ensure that electronic media errors and failures are quickly remedied so that patient health information is recovered accurately and intact. One final technical safeguard is network, or transmission security that ensures HIPAA compliant hosts protect against unauthorized access to ePHI. This safeguard addresses all methods of data transmission, including email, internet, or private networks, such as a private cloud.
To help ensure HIPAA compliance, the U.S. government passed a supplemental act, The Health Information Technology for Economic and Clinical Health (HITECH) Act, which raises penalties for health organizations that violate HIPAA Privacy and Security Rules. The HITECH Act was put into place due to the development of health technology and the increased use, storage, and transmission of electronic health information.
Data Protection for Healthcare Organizations and Meeting HIPAA Compliance
The need for data security has grown with the increase in the use and sharing of electronic patient data. Today, high-quality care requires healthcare organizations to meet this accelerated demand for data while complying with HIPAA regulations and protecting PHI. Having a data protection strategy in place allows healthcare organizations to:
- Ensure the security and availability of PHI to maintain the trust of practitioners and patients
- Meet HIPAA and HITECH regulations for access, audit, integrity controls, data transmission, and device security
- Maintain greater visibility and control of sensitive data throughout the organization
The best data protection solutions recognize and protect patient data in all forms, including structured and unstructured data, emails, documents, and scans, while allowing healthcare providers to share data securely to ensure the best possible patient care. Patients entrust their data to healthcare organizations, and it is the duty of these organizations to take care of their protected health information. To learn more about best practices for healthcare data protection, read our guide to healthcare cybersecurity.
HIPAA Compliance with Fortra DLP
See how Fortra DLP for HIPAA compliance locates and protects sensitive patient data throughout the integrated delivery network.
HIPAA Compliance in the COVID-19 Landscape
It’s an understatement to say the world has changed as a result of the COVID-19 pandemic. Healthcare has and, almost undoubtedly, will continue to change the most over the next several years. Maintaining privacy compliance for private health information has already proven to be more difficult, with risk factors to such data including:
- Telehealth Visits: The number of healthcare provider visits conducted over the web has skyrocketed. Patients who typically make short trips to the clinic or office decide to stay home and see their physician virtually, unless an in-person visit is absolutely necessary. Data protection over the Internet is difficult if proper precautions are overlooked.
- Increased Patient Count (post-lockdown): Now that many states allow most procedures and visits to occur, there has been an onslaught of appointments. When paired with physical distancing guidelines, offices are often short on staff when schedules are maxed out. This situation creates an opportunity for HIPAA compliance mistakes.
- Multiple Care Providers: Patients often see multiple doctors. However, increased testing and varied result times make things cloudy. Primary care physicians receiving updates from multiple testing labs, patients, or hospitals means data is moving in and out at a faster pace (if dealing with potential virus cases).
Stay Up-to-Date to Avoid Compliance Lapses
The Department of Health and Human Services (HHS) has proactively updated those who fall under HIPAA coverage (aka, “covered entities”). Here’s what the HHS has to say about the increase in telehealth options:
“A covered health care provider that wants to use audio or video communication technology to provide telehealth to patients during the COVID-19 nationwide public health emergency can use any non-public facing remote communication product that is available to communicate with patients. OCR is exercising its enforcement discretion by not imposing penalties for noncompliance with the HIPAA Rules in connection with the good faith provision of telehealth using such non-public facing audio or video communication products during the COVID-19 nationwide public health emergency. This exercise of discretion applies to telehealth provided for any reason, regardless of whether the telehealth service is related to the diagnosis and treatment of health conditions related to COVID-19.” (Source: HHS)
Make sure to follow these updates from those who monitor and enforce HIPAA compliance in order to ensure the safest environment. Communications are likely to provide guidance on the most prominent issues caused by the pandemic, such as increased appointments, data threats, and mitigation techniques.
The Most Recent HIPAA Updates (2024-2025)
After experiencing mounting pressure to implement a more substantial update to HIPAA, HHS’ Office for Civil Rights (OCR) issued a Notice of Proposed Rulemaking (NPRM) in 2020 to make a myriad of changes to the HIPAA Privacy Rule. Just over four years later, in January 2025, the OCR then proposed a significant update to the HIPAA Security Rule.
Proposed HIPAA Security Rule Update
The first major HIPAA Security Rule update since 2013 was published in the Federal Register on January 6, 2025. The rule addresses growing cybersecurity threats following 747 large healthcare data breaches in 2023, with key requirements including:
- Asset management: Annual technology inventory and network mapping
- Enhanced risk analysis: Specific threat and vulnerability identification requirements
- Mandatory encryption: Applies to all ePHI at rest and in transit
- Multi-factor authentication and network segmentation
- Regular testing: Bi-annual vulnerability scans & annual penetration tests
- Incident response: Data restoration procedures within 72 hours
- Business associate oversight: Annual security verification
The rule additionally eliminates "required" vs. "addressable" distinctions, making all cybersecurity requirements mandatory.
HIPAA Privacy Rule Modernization
Originally proposed in 2020, comprehensive Privacy Rule updates remain under consideration, but a final rule could be issued in 2025 under the second Trump administration. Some expected changes include:
- Faster PHI access: Reduce patient PHI access timeframes from 30 to 15 days
- Enhanced inspection rights: Allow patients to photograph medical records
- Fee transparency: Require posted fee schedules for PHI access
- Expanded care coordination: Broaden healthcare operations definition
- Threat disclosure: Expand PHI disclosure when harm is "reasonably foreseeable" (vs. "imminent")
- Good faith standard: Permit PHI uses based on individual's best interest
- Streamlined processes: Eliminate written Notice of Privacy Practices acknowledgment
Other HIPAA Changes
Administrative Simplification: This December 2024 rule modified pharmacy standards to improve data exchange and reduce compliance burdens.
Reproductive Health Privacy: This 2024 rule strengthening reproductive health information privacy was vacated nationally in 2025 following legal challenge.
Types of HIPAA Violations
The Department of Health and Human Services (DHHS) has identified five common types of HIPAA violations that fall under the Enforcement Rule, allowing the department to establish procedures for investigations and hearings related to the violation(s), mandate corrective measures for the violating entity, and impose civil monetary penalties:
Fortra's Cyber Solutions Are HIPAA-Compliance-Ready
Fortra's extensive portfolio of cybersecurity solutions protect your organization's sensitive health data wherever it lives and moves, extending traditional endpoint security to the cloud. Chat with our experts to learn how our solutions will enhance your security posture, keep you HIPAA-compliant, and keep your most sensitive data in the right hands.