Cloud-Delivered Analytics, Workflows, and Reporting for No-Compromise Data Protection
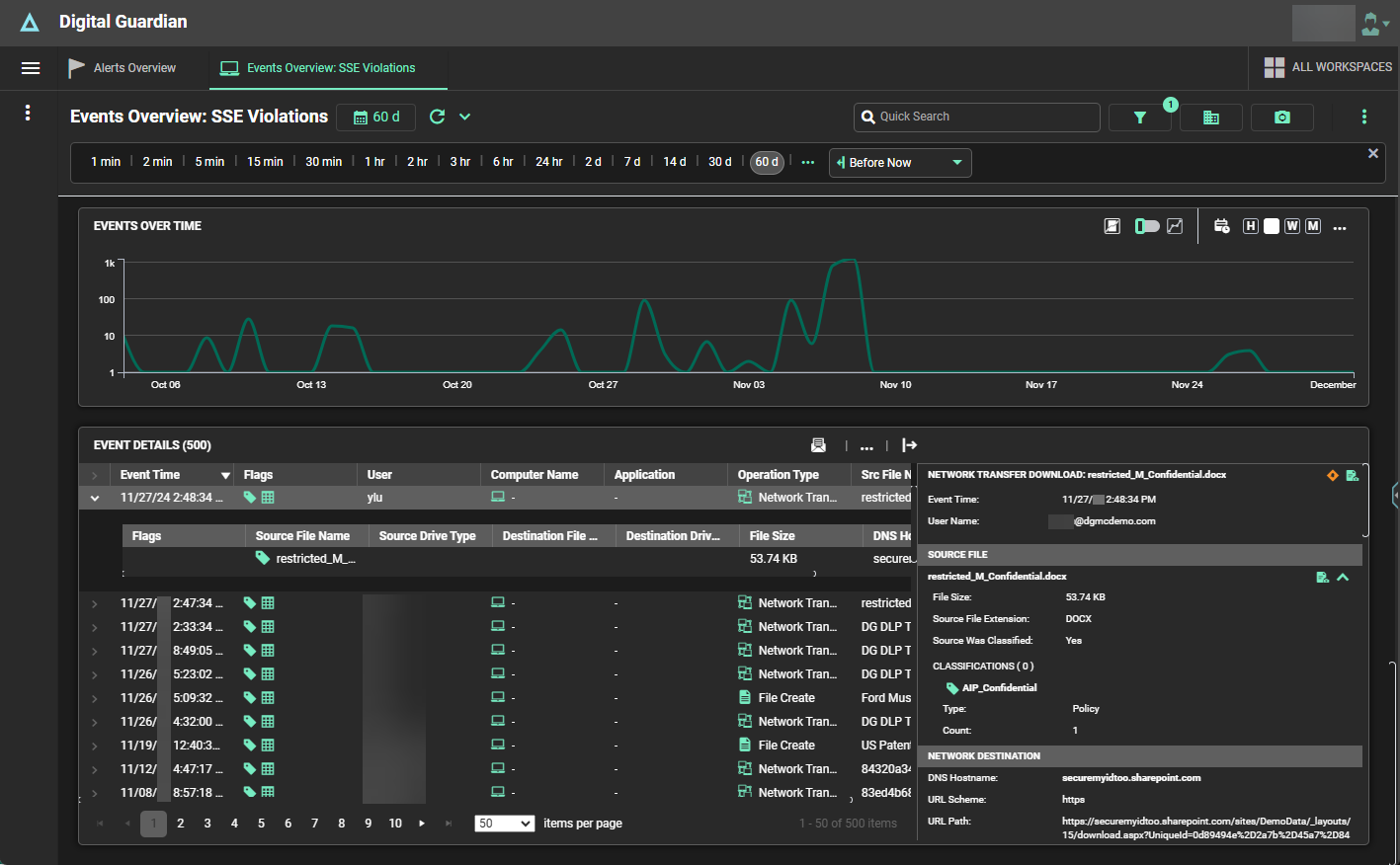
Powered by Amazon AWS, Digital Guardian's Analytics & Reporting Cloud (ARC) correlates and analyzes system, user, and data events from endpoint agents and network appliances to provide the visibility and context you need to identify and remediate insider and outsider threats.
Key Features
Deep visibility into system, user, and data events—including historical detection
Focus on high-fidelity events and analytics
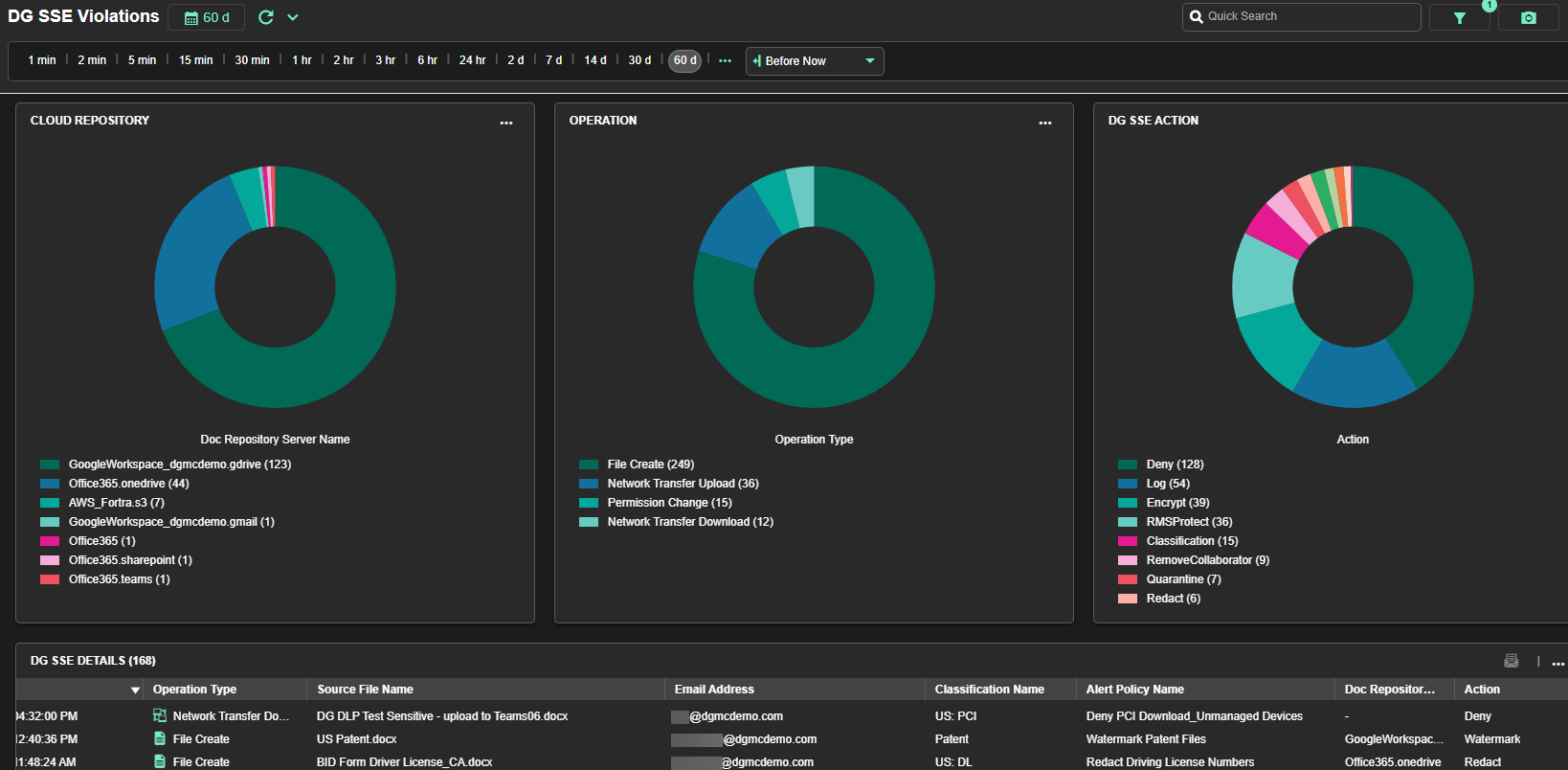
Integrated Secure Service Edge (SSE) and Endpoint Detection & Response (EDR)
Threat intelligence insights from the Fortra Threat Brain
Workspaces developed and approved by analysts and threat hunters
Thorough risk identification and assessment via behavior-based rules and contextual intelligence
Manual and automated policy enforcement capabilities
Intuitive incident management
Cloud-based, scalable SaaS architecture (powered by AWS)

Analytics & Reporting Cloud Benefits
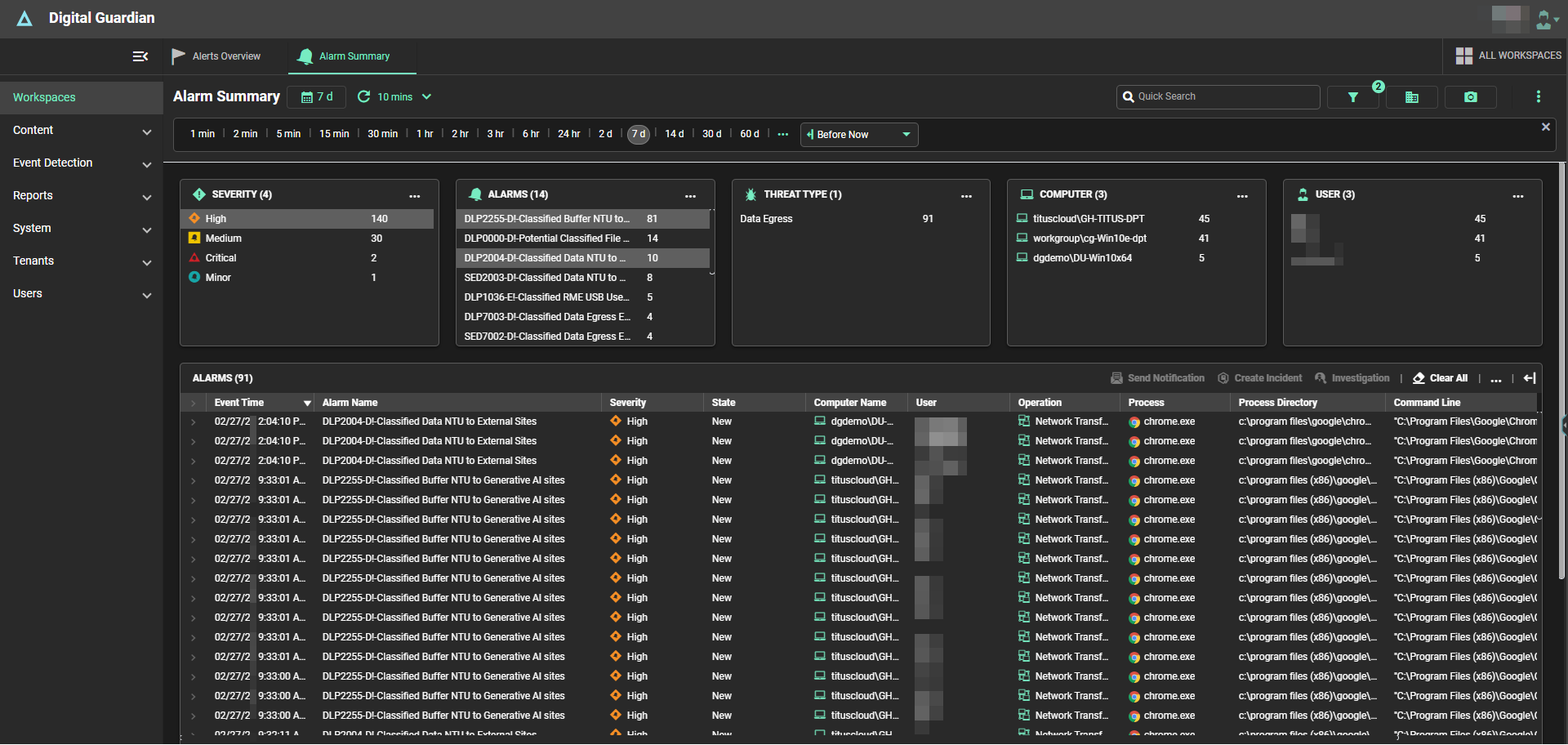
Analytics that Filter Out Noise
Monitor the most comprehensive set of your system, user, and data-triggered events. Alarms are only triggered for high-fidelity events that warrant additional investigation.
Security Analyst-Approved Workspaces
Our user-friendly workspaces—developed by experienced threat hunters, infosec analysts, and incident responders—guide security professionals to high-fidelity events requiring the most immediate remediation. As your analysts determine next steps in their response efforts, they can create custom dashboards and reports that give actionable insights to make more informed decisions.

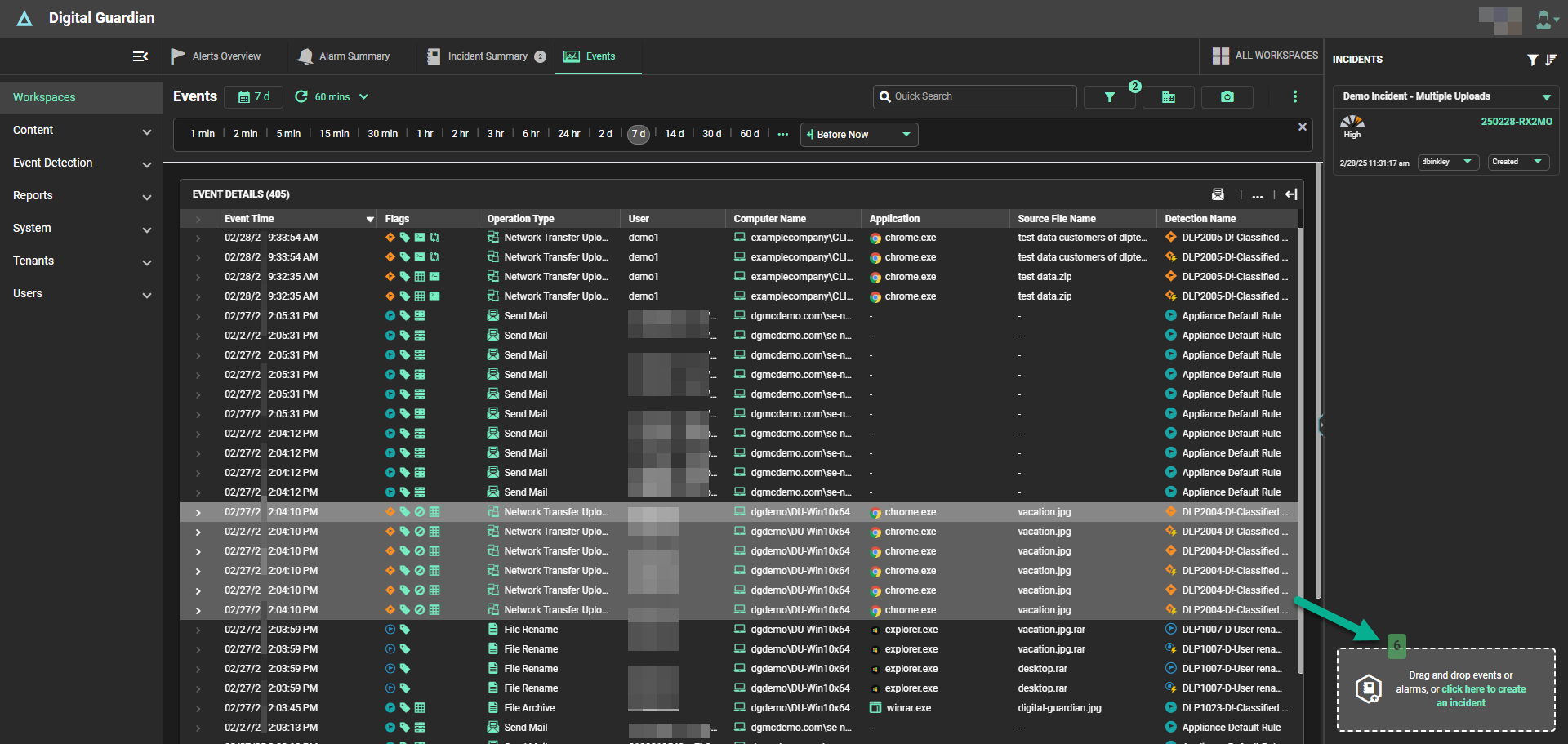
Drag-and-Drop Incident Management
Simply drag and drop to create new events, artifacts, and alarms. Your visually concise incident timeline will automatically be built out, after which you can add comments as you investigate. Our user experience allows teams to swiftly identify threats and their associated risk, accelerate their investigations, and simplify compliance.
Right Click to Remediate in Real Time
Remediate security events from any screen, in real time by enforcing data protection policies and automating and/or blacklisting processes across the enterprise. Options include blacklist, scan, warn on launch, send to VirusTotal, and more.
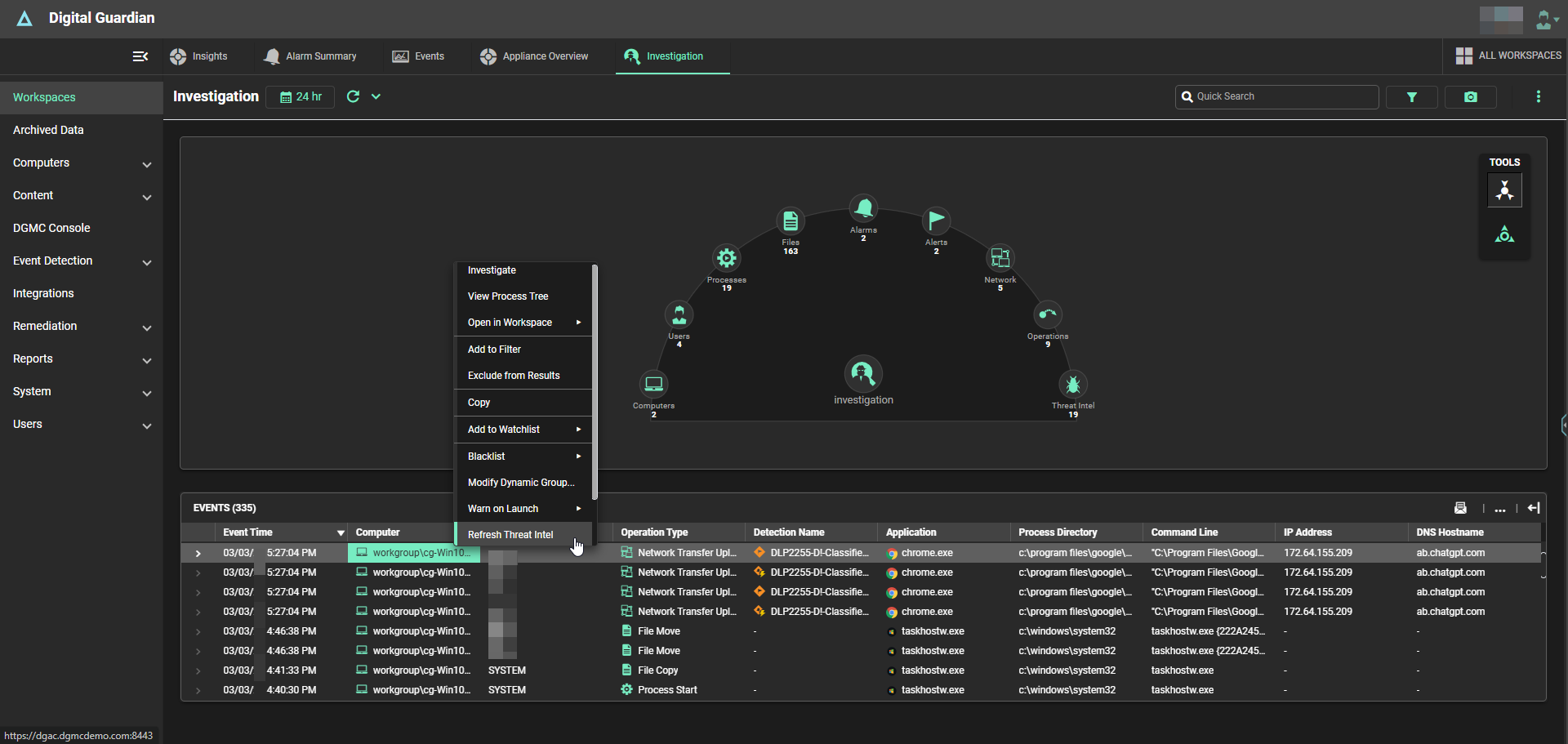
SSE, EDR, and Fortra Threat Brain Integrations
By integrating world-class threat intelligence insights from the Fortra Threat Brain along with the data protection and incident remediation capabilities of Secure Service Edge (SSE) and Endpoint Detection & Response (EDR), respectively, Digital Guardian significantly simplifies security programs by unifying what would normally be several separate tools within a single agent and console. These integrations also facilitate centralized, full-spectrum threat detection and neutralization.
See ARC in Action with a Digital Guardian On-Demand Demo
Discover how Digital Guardian’s Analytics & Reporting Cloud (ARC) delivers real-time event insights, user-friendly workspaces for streamlined incident investigation and remediation, inherent reporting capabilities for maintaining regulatory compliance, and more.
What Sets ARC Apart?
No Hidden Costs
In-House Managed Services
SSE & EDR Integrations
Advanced Threat Intelligence
Inherent Reporting
Integrated Customer Support
What Our Customers Are Saying
Resources
Dive Into Industry-Leading Analytics & Reporting Capabilities
Digital Guardian provides no-compromise data protection that stops data loss in its tracks—all through a scalable, cloud-delivered DLP platform that keeps up as your organization evolves.
Ready to learn how Digital Guardian can improve your security posture? Request a live demo for a full rundown with our security experts.