Here's the Challenge
All manufacturers must have strategies in place to ensure the free flow of information across their supply chains but must also safeguard that information from industrial espionage, nation-state adversaries, and malicious insiders. Manufacturers are also under pressure to meet increasingly stringent export requirements such as the International Traffic in Arms Regulations (ITAR) and Export Administration Regulations (EAR).
Manufacturers' most valuable IP often comes in the form of unstructured data, such as CAD files, source code, and formulas. The problem is that most data loss prevention solutions aren’t very good at protecting, let alone recognizing this unstructured data.
Here's the Solution
Over 75 manufacturing organizations—including four of the top eight best-selling automotive brands—trust Fortra’s Digital Guardian to stop IP theft and help them share data securely across their supply chain.
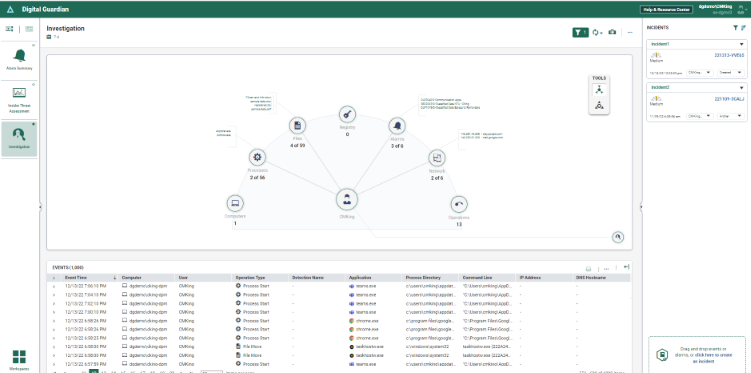
Our data loss prevention (DLP) platform enables manufacturers across the globe to effectively discover, monitor, and control sensitive design data, whether it’s on the network, in use on desktops or laptops, at rest in databases or network servers, or stored in the cloud. Our solution, powered by AWS, enables organizations to quickly identify threats to their data and critical results thanks to a series of out-of-the-box dashboards and an integrated rapid start-up. Real-time user prompts enhance security awareness as soon as a potentially unsafe action is taken, reducing insider misuse of sensitive data.
Need to share data across multiple factories and ensure that trade secrets don't fall into the wrong hands? Digital Guardian Secure Collaboration allows you to securely share your intellectual property and trade secrets both internally and with external entities.
Benefits of DLP
Improve Your Organization’s Security Posture
Comply With Key Regulatory Requirements
With the ability to compile a detailed audit trail, Digital Guardian can demonstrate compliance with International Traffic in Arms Regulations (ITAR), Export Administration Regulations (EAR), and other current regulatory requirements—and provides the flexibility to meet future needs as regulatory requirements change. Our DLP platform will help manufacturers protect:
Why Top Manufacturers Choose Digital Guardian
Identify, Track, and Share Your Sensitive Data With Confidence
Security teams in the manufacturing sector are often forced to balance two competing demands: securing intellectual property and enabling high-speed production efficiency.
Your team is laser-focused on protecting your organization’s research and development processes to maintain its competitive edge, including your product designs, manufacturing specifications, and supplier contracts. To ship successful products, however, the business must share highly confidential information throughout the supply chain, including with third parties outside of the organization and employees who may not necessarily be with your organization forever.
As a result, finding ways to control how suppliers consume our sensitive designs, prevent leaks to unauthorized partners or competitors, audit your data throughout the supply chain, and revoke specific individuals' access to proprietary data are often at the top of security leaders' minds at manufacturing organizations.
Our solution is Digital Guardian Secure Collaboration, which lets you identify, safeguard, and secure your IP, trade secrets, and export-regulated data wherever it travels. This means you can share your sensitive data across your supply chain with confidence, without changing how you work.
“Fortra was the only company that could secure all file types, including atypical files such as Adobe Illustrator, and work with multiple platforms. Our users have a seamless experience, so their workflow isn’t hindered, and we’re actively looking to expand our deployment across more areas of the Company.”
Learn more about how this large footwear & apparel manufacturer successfully deployed Digital Guardian Secure Collaboration, which afforded them more control over their data in a large, cross-platform environment.
Manufacturing DLP Resources
We've learned a lot over the years from working with top manufacturers to secure their most sensitive data. Gain insight into our wealth of experience by reading our top tips on IP protection from a Fortune 100 CISO, our manufacturer's guide to protecting trade secrets, and one of our top manufacturing case studies.
Schedule a Demo
Ready to see our DLP platform in action? See how Digital Guardian can help protect your critical data wherever it lives.