The U.S. government, in tandem with officials in nine other countries, have taken down yet another massive Business Email Compromise (BEC) scam, this one involving the theft of 250,000 identities and more than 10,000 phony tax returns.
BEC scams have been cutthroat over the last several years, responsible for billions of dollars in fraud. The FBI said in April that in 2018 alone it received 351,000 BEC scam complaints totaling $1.2 billion in losses, almost half of victim losses reported to the FBI's Internet Crime Complaint Center.
We learned this week that BEC scams have accounted for at least $26 billion in losses between June 2016 and July 2019.
The most recent one, disclosed Tuesday, relied on the assistance of 281 individuals, 74 based in the U.S. to trick unsuspecting victims into wiring them funds.
According to the Department of Justice, as part of the scheme, the criminals attempted to extract more than $91 million in refunds via tax returns. Some of that money that was laundered and spent on goods, including in one scenario, a 2019 Range Rover Velar S,
Cracking down on the scammers involved a series of efforts, including a dizzying 214 domestic actions, including arrests, warning letters sent to money mules, asset seizures, and the seizure of $3.7 million.
According to the indictment, a community college, an energy company, a Georgia-based health care provider, in addition to unnamed title companies, corporations, and individuals, were all implicated in the scam and tricked into misdirecting funds.
As part of the operation, something the FBI and the DoJ’s International Organized Crime Intelligence and Operations Center (IOC-2) dubbed Operation reWired, the agencies worked with a handful of U.S. government entities, including the U.S. Department of Homeland Security, U.S. Department of the Treasury, U.S. Postal Inspection Service, and the U.S. Department of State.. It also worked with law enforcement in Nigeria, where 167 cybercriminals were arrested, Turkey, Ghana, France, Italy, Japan, Kenya, Malaysia, and the United Kingdom.
“We will continue to work with our international, federal and state partners to pursue all those responsible for perpetrating this fraud, preying on innocent victims and attempting to cheat the U.S. out of millions of dollars," Chief Don Fort of IRS' Criminal Investigation team, said this week of the departments' efforts.
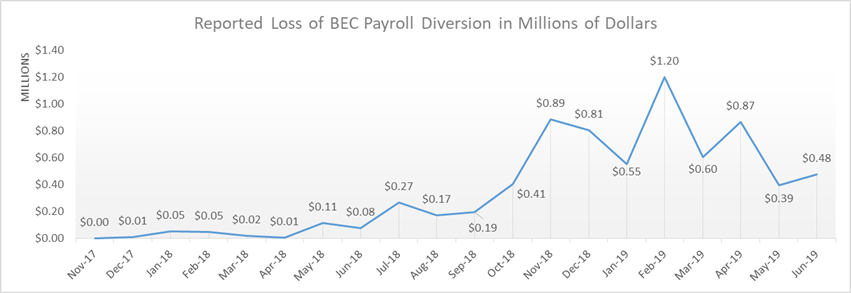
As hinted previously, the FBI and DoJ’s news comes the same week that the FBI published a Public Service Announcement around BEC scam statistics. According to the agency, between May 2018 and July 2019, there was a 100 percent increase in identified global exposed losses, with scams being reported across all 50 states and 177 countries.
To protect themselves, the FBI is encouraging employees, if they haven't already, to familiarize themselves with the tell-tale signs of a BEC scam, in addition to following these tips:
- Use secondary channels or two-factor authentication to verify requests for changes in account information.
- Ensure the URL in emails is associated with the business it claims to be from.
- Be alert to hyperlinks that may contain misspellings of the actual domain name.
- Refrain from supplying login credentials or PII in response to any emails.
- Monitor their personal financial accounts on a regular basis for irregularities, such as missing deposits.
- Keep all software patches on and all systems updated.
- Verify the email address used to send emails, especially when using a mobile or handheld device by ensuring the senders address email address appears to match who it is coming from.
- Ensure the settings the employees’ computer are enabled to allow full email extensions to be viewed.
Piggybank photo courtesy kredite.org
