New Disruptive Technology Strike Force to Fight Back Against Foreign Governments That Steal Data
The goal of a new government task force is to block foreign adversaries from siphoning sensitive data.
Friday Five: New Guidance for At-Home Employees, Ransomware Demands Evolving, & Emerging Vulnerabilities
The White House and NSA are releasing new security guidance for organizations and employees alike, but ransomware and new vulnerabilities remain dangerous. Read about all the latest in this week’s Friday Five.
U.S. GAO Outlines Key Practices for Improving Data Privacy Programs in the Federal Sector
A U.S. agency has offered four tips for the U.S. government to improve federal efforts to protect privacy and sensitive data.
Friday Five: Dark Web Revenue Falling, Pig Butchering Scams and Other Attacks on the Rise, & Critical Infrastructure at Risk
The dark web isn’t what it once was with Hydra, but cybercriminals are staying busy with ransomware, targeted attacks against developers, and more. Catch up on all these stories and more in this week’s Friday Five!
Friday Five: Cyber Gang Members Sanctioned, a Cybercrime Messaging Platform, & Stricter Security Regulations
This week saw the takedown of a cybercrime messaging platform, sanctions imposed on TrickBot members, the release of a recovery script for ransomware victims, and more. Catch up on the latest news in this week's Friday Five!
The Most Overlooked Elements of Preventing Cyberattacks Businesses Should be Aware of
To help defenders close the gaps, we asked more than 30 experts what the most overlooked element of preventing cyberattacks is.
Friday Five 1/27
A ransomware giant was taken down this past week, but vulnerabilities, poor cybersecurity implementation, and new hacking methods remain. Catch up on all of the latest stories in this week’s Friday Five!
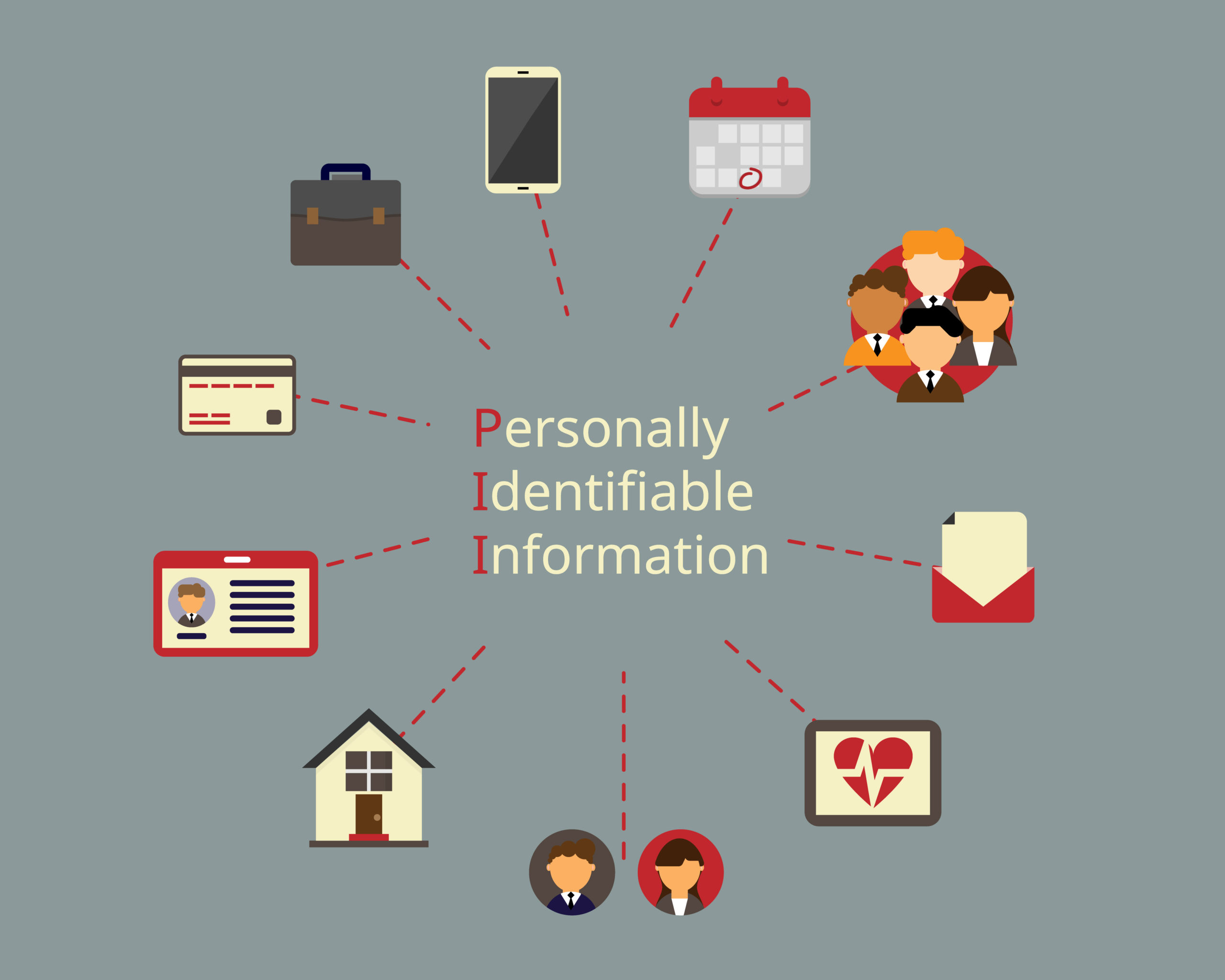
PII Compliance Checklist: How to Protect Private Data
In this era of heightened data privacy, organizations, especially those in highly regulated industries, need to maintain a PII compliance checklist to protect private data in their possession.
Top Tips for Businesses Looking to Prevent IP Theft
To learn more about how to curb intellectual property theft, we reached out to a panel of intellectual property experts and business leaders for their best tips.
How to Prevent Third-Party Vendor Breaches
As organizations continue to rely on third-party technologies, third-party breaches have become common. One of the key ways to prevent third-party vendor breaches is to monitor your attack surface continuously.
What Is a Third-Party Breach?
As the name suggests, third-party data breaches are security violations caused by third-party contractors, vendors, and other businesses affiliated with an organization.
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!