Friday Five: The Fight to Secure Critical Infrastructure, AI's Double-Edged Sword, & More
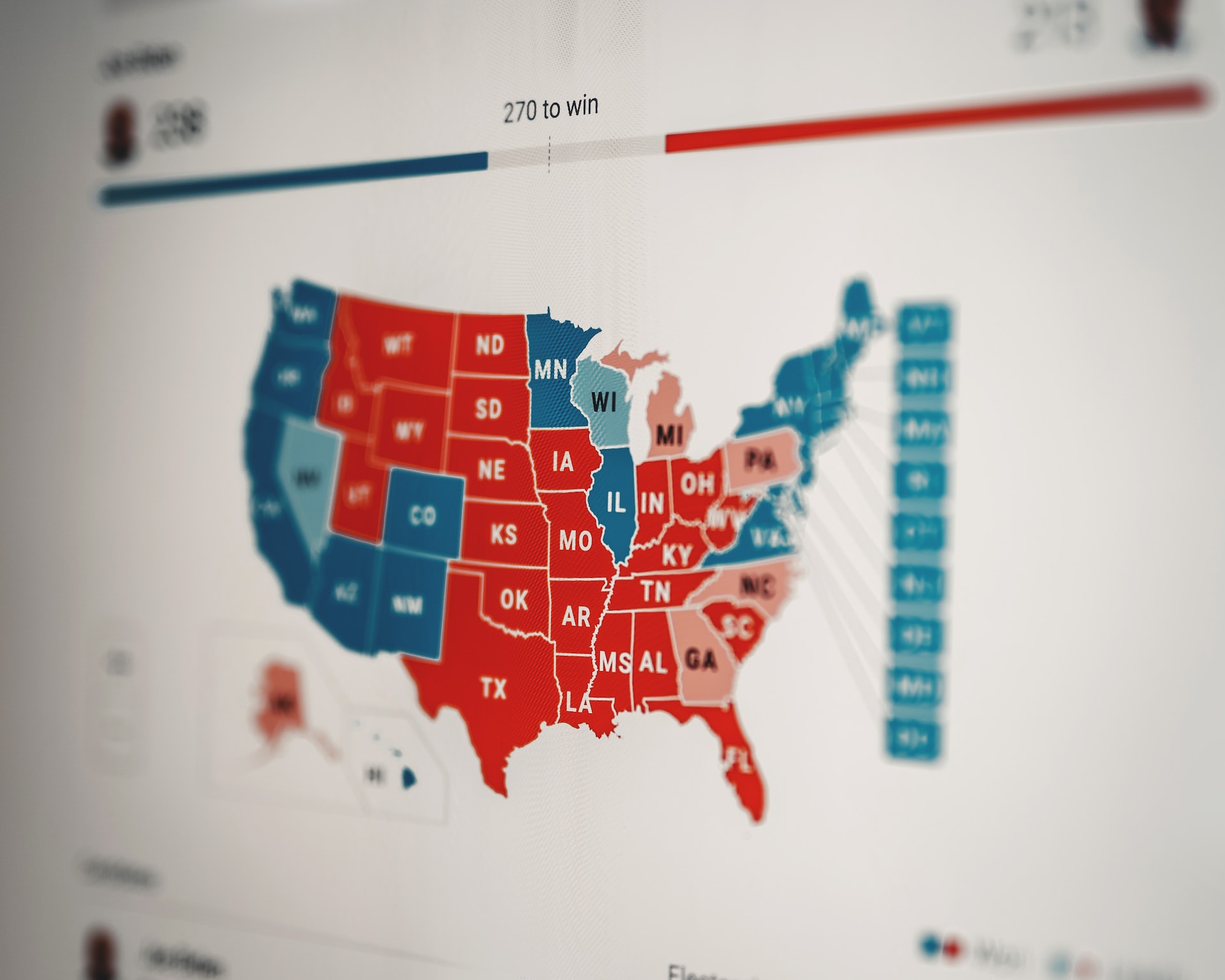
In this week's Friday Five, read about agencies' improving cyber threat-sharing capabilities, the ongoing fight to secure critical infrastructure, election interference concerns, and more.
What is the New Swiss Data Protection Act, and How Do You Achieve Compliance?
Switzerland's revised data protection law took effect September 2023. What are the implications of the law and how can organizations comply with what it asks? We dig into it in today's blog.
What Is a Data Governance Policy & How to Write One
Having a strong data governance policy can help your organization ensure data accuracy, consistency, and security across your organization but what are the first steps to writing one?
Friday Five: Data Security Challenges in 2024, Compliance Updates, & More
In 2024's first edition of our Friday Five series, learn about CMMC updates and other data security challenges to come, new malware, and a ransomware decryptor that can help victims.
What Is Data Protection? Principles, Strategies & Trends
What is data protection and what makes it different from data security and data privacy? We answer those questions and give pointers on how to develop a data protection strategy in this blog.
Data Scanning: How to Protect Sensitive & Confidential Data
Being able to scan your data can give you the full scope of where files exist and what needs to be properly secured. In this blog, we break down why it's a key part of data loss prevention, who uses data scanning, and why it's important.
How Do Data Compromises Happen? And How to Prevent Them
Understand what a data compromise is, how they happen, what they typically target, and tips for preventing a data compromise from happening in the first place in our new blog.
Everything You Need to Know About Microsoft DLP
Microsoft DLP, part of the larger Purview offering, can be a part of your organization's defensive strategy and complemented by Digital Guardian's enhanced offering.
Friday Five: Tried and True Scamming Tactics, AI Risks, & More
In this week's Friday Five, learn about how threat actors are weaponizing OAuth apps, QR codes, and Google Forms; why AI could increasingly create security and compliance risks; and more.
Top Data Vulnerabilities that Cause Data Loss
In this blog we take a high level look at some of the vulnerabilities or flaws in a system that can lead to data loss, the stages of exploiting a vulnerability, the impact, and how to best safeguard your data against vulnerabilities.
Don't Fall Behind
Get the latest security insights
delivered to your inbox each week.
Thank you for subscribing!