NETWORK DLP
Protect Sensitive Data on the Move to Support Regulatory Compliance
WHAT IS IT?
Network DLP without the complexity.
Digital Guardian Network DLP helps support compliance and reduce risks of data loss by monitoring and controlling the flow of sensitive data via the network, email or web. It is typically deployed in a matter of hours and does not require a dedicated resource once it is deployed.
Our network DLP appliances inspect all network traffic then enforce policies to ensure protection. Policy actions include: allow, block, encrypt, reroute, and quarantine.

✓ Monitors and protects all network traffic
✓ Flexible, tailored responses
✓ Accelerates compliance efforts, securely
![]()
Monitors and protects all network traffic
DG Network DLP monitors and controls all communications channels – including email, Web, File Transfer Protocol, Secure Sockets Layer, and applications such as webmail, blogs, and other social media to keep your data secure.
![]()
Flexible, tailored responses
Using our configuration wizard, you can easily create automated responses tailored for your environment and culture. Policy based actions include: allow, block, encrypt, reroute, and quarantine. User notification at the time of potentially risky behavior reinforces desired data handling procedures.
![]()
Accelerates compliance efforts, securely
Digital Guardian Network DLP can be deployed, configured and protecting data in just a few hours. Pre-configured policies for PII, PHI, and PCI, along with the flexibility to create customized policies with our wizard, ensure you protect what matters most to your organization and support compliance needs. Reports provide a detailed picture of sensitive and regulated data movement for audits.

Your Trusted Partner
in Data Protection
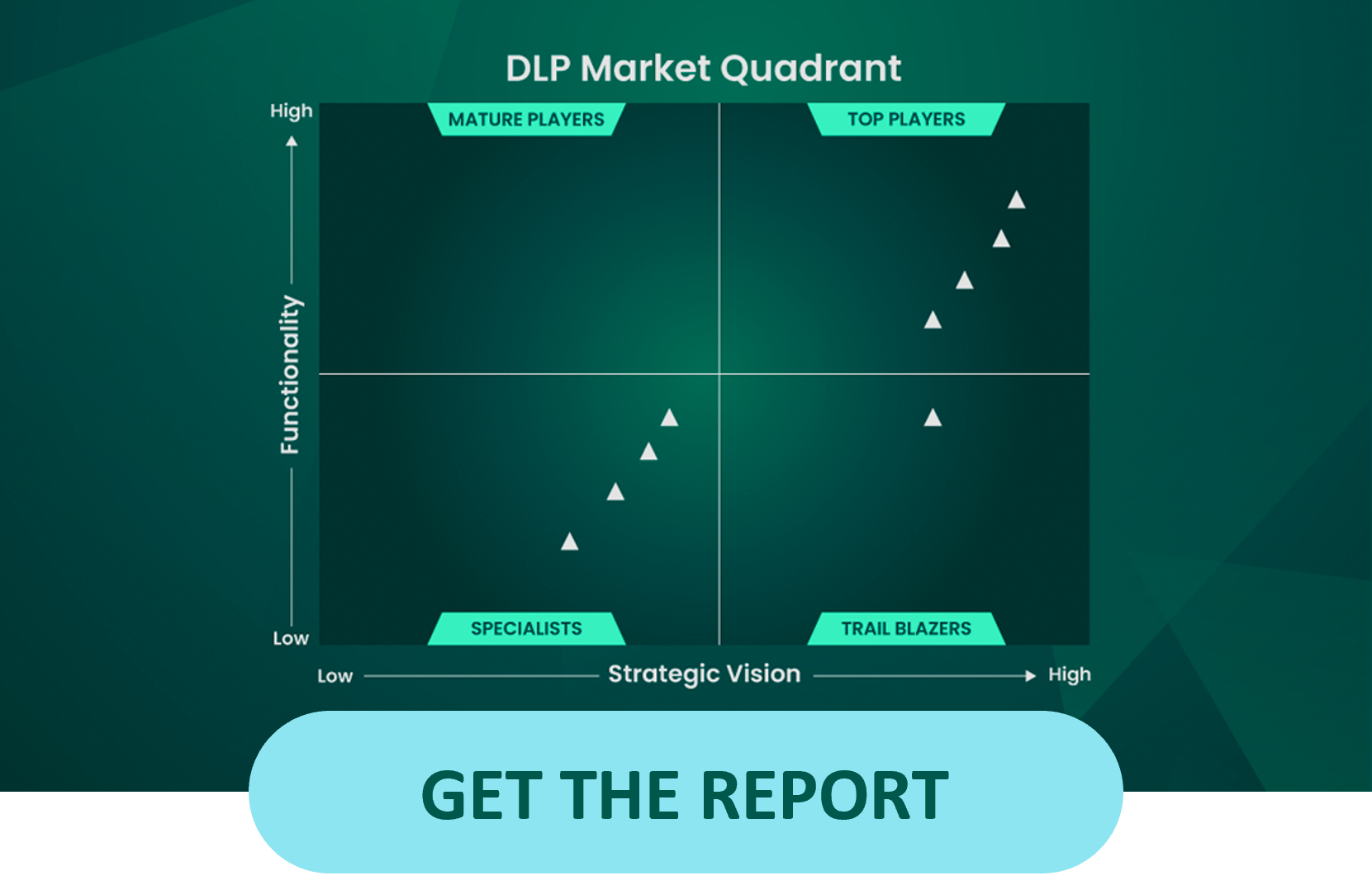
DLP Market Quadrant Leader
Protecting Over 5,000,000 Endpoints
From Mid-Market to Enterprise
- Deepest visibility
- Support compliance efforts
- Protect data in hours, not days
- Customized policies
- Safeguard PII, PHI, and PCI
- Supports data discovery
- Reduces false negatives
- Enables cloud data protection
- Monitor and control the flow of data
- Flexible responses
- Regularly audit data movements
- Keep your data secure
- See data movement for audits
- Inspect all network traffic
- Reduces ongoing maintenance
- Minimal configuration
CASE STUDIES & RESOURCES
FEATURED USE CASE
Securing New England Federal Credit
Union’s Members' PII
NEFCU selected Fortra's Digital Guardian® (DG)
Network DLP for its simplicity, cost effectiveness
and completeness of functionality in its architecture.
WHY DIGITAL GUARDIAN?
Simplified Setup and Management
Our appliance-based approach speeds deployment and reduces ongoing maintenance. The appliance ships with pre-configured policies for common data types including PII, PHI, and PCI, and can be inserted into your existing infrastructure with minimal configuration. It’s typically deployed in a matter of hours. And it doesn’t require a dedicated resource once it’s deployed.
Highest Accuracy = Lowest False Alarms
Digital Guardian’s Database Record Matching (DBRM) delivers the accuracy needed to reduce false positives and false negatives. DBRM recognizes, registers and protects a wide range of both structured (e.g. fields in databases or columns in spreadsheets) and unstructured data types (e.g. document formats such as Microsoft Office, source code and PDF files).
Appliance Options
Our network appliance can be deployed as a physical machine, a virtual machine, or as an image in cloud services like Microsoft Azure giving you the flexibility required to maximize existing investments or migrate your business.